Quick Guide
This short introductory section is intended to help with understanding the basic layout of the user interface, terminology and visual indicators that are used on the Spectra Analyze appliance and in its documentation.
Global Header Bar
At the top of the Spectra Analyze interface is the global header bar, containing the most commonly used options and the main appliance menu used to access all sections of the appliance.
The first item from the left, after the logo, is the Search Samples box, a text field where users can enter search queries and get a pull-down list of all supported keywords. For more information on this feature, refer to the Advanced Search page. Clicking on the text field will expand it to the far right of the header bar and hide other menu items to provide more space for typing and constructing the query. Clicking away from the text field will remove the focus and restore the original menu layout. Performing the search will navigate the users to the Advanced Search page to display results.
To the right of the Search Samples box is the Upload button, allowing a quick way to upload samples and submit URLs to the appliance from any page of the interface. An upload status bar will be displayed in the header bar while files are uploading. Navigating away from the page or refreshing the browser tab during upload is not supported and will trigger a warning that the upload will be lost. For more information on uploading samples, submitting URLs, file privacy and size limitations, refer to the File Submissions page.
- Dashboard: The Dashboard displays statistics related to the amount and type of files that have been submitted and processed on the appliance within a specified time range.
- Search: The Advanced Search feature introduces rich metadata search capabilities on the Spectra Analyze appliance, makes it easier to search across large data sets (both local and global in ReversingLabs Spectra Intelligence), and enables faster, more powerful malware discovery with increased coverage. Click here for more information on writing advanced search queries.
- YARA: Allows rule-based identification and classification of files. Users can create their own YARA rules containing textual or binary patterns. When a file matches the pattern found in a YARA rule, it receives the classification defined by that rule. YARA rules can be grouped into rulesets. (Note: If this page is not visible in the header bar, it can be assigned to the user through the Administration > User Role configuration page.)
- Graph: The Graph page provides an interactive visualization of relationships between malware samples, files, domains, IPs, and other entities.
- Quota Indicator: Clicking the pie-chart icon opens a pop-up listing all ReversingLabs APIs in use on the appliance which have a limited quota, and their current status.
- Alerts Indicator: The Alerts feature allows real-time monitoring to track changes in malware classification and analysis results. It automates notifications for specific events, allowing users to utilize their time more efficiently and be informed of malware status changes on-the-go. Clicking the indicator opens a list of recent Alerts. If there are any unresolved alerts, their count is displayed as a red badge on the indicator.
- Help: Contains options to access the appliance documentation, contact ReversingLabs support, and open the methodology / legend pop-up with basic information about Risk Score.
- User menu: Shows the username of the current user, contains links to the Administration and User Profile (edit user information, change credentials, manage alerts ) pages, and the option to Log Out from the appliance.
Health Status Indicator
The second to last item in the main appliance menu is the health status indicator, pointing out issues with the system load and showing if the appliance is connected to a file reputation service, and if the service is reachable or not. Administrators can click the icon to open a pop-up with a more granular look at the system resources: Disk Usage, Memory usage, CPU utilization, outstanding alerts and issues, and Spectra Detect Manager connection status. The pop-up also contains a link to Open System Status page with detailed information on all the system monitoring services.
Thresholds for these services, such as CPU/memory/disk usage or queue sizes, are configured on the Administration > Configuration > System Health Indicator page.
If there are no issues with the system load and if the appliance is connected to Spectra Intelligence or the T1000 File Reputation Appliance, this will be indicated by a black icon.
A red icon with a small exclamation mark means that the reputation service is not configured or reachable or that CPU/memory/disk usage or queue sizes went over the configured thresholds. In this case, hovering over the icon will list the detected issues.
The services used to deliver file reputation data (Spectra Intelligence or T1000 File Reputation Appliance) can be configured in the Spectra Intelligence / T1000 File Reputation Appliance dialogs in the Administration > Configuration section.
Color-Coding and Sample Status
The Spectra Analyze interface makes use of consistent color-coding to indicate sample classification and risk. There are four colors, each one corresponding to a different sample status. The sample status indicates whether the file is goodware, suspicious or malicious - or if no threats were found, indicating the sample remains unclassified.
In addition to color-coding, certain parts of the UI also indicate classification status of submitted files and URLs by colored symbols: red square is malicious, orange rhombus is suspicious, green circle is goodware, dark gray square with a circle cutout is no threats found.
Inside each of the symbols is the sample’s risk score. Samples with no threats found (samples without classification) don’t have a risk score.
Samples with a risk score of 5 are represented using a unique icon, as the indicators found during analysis were deemed insufficient to classify the file as definitively malicious or benign. These samples may be of interest, as they have a higher chance of changing classification and/or risk factor as soon as any new information becomes available.
Some Spectra Analyze APIs return sample classification as a numerical value.
| Classification | Value |
|---|---|
| No threats found | 0 |
| Goodware | 1 |
| Suspicious | 2 |
| Malicious | 3 |
Read more about the ReversingLabs classification algorithm.
Where to Find Visual Indicators of Sample Status?
Color-coded indicators are present in the following parts of the interface, indicating sample status:
- On the YARA page – statistics about ruleset matches
Inside each of the symbols is the sample’s risk score. Samples with no threats found (samples without classification) don’t have a risk score.
- Sample Details page – as the background color of the Summary header section. The Risk Score numerical value is also indicated in the Summary section
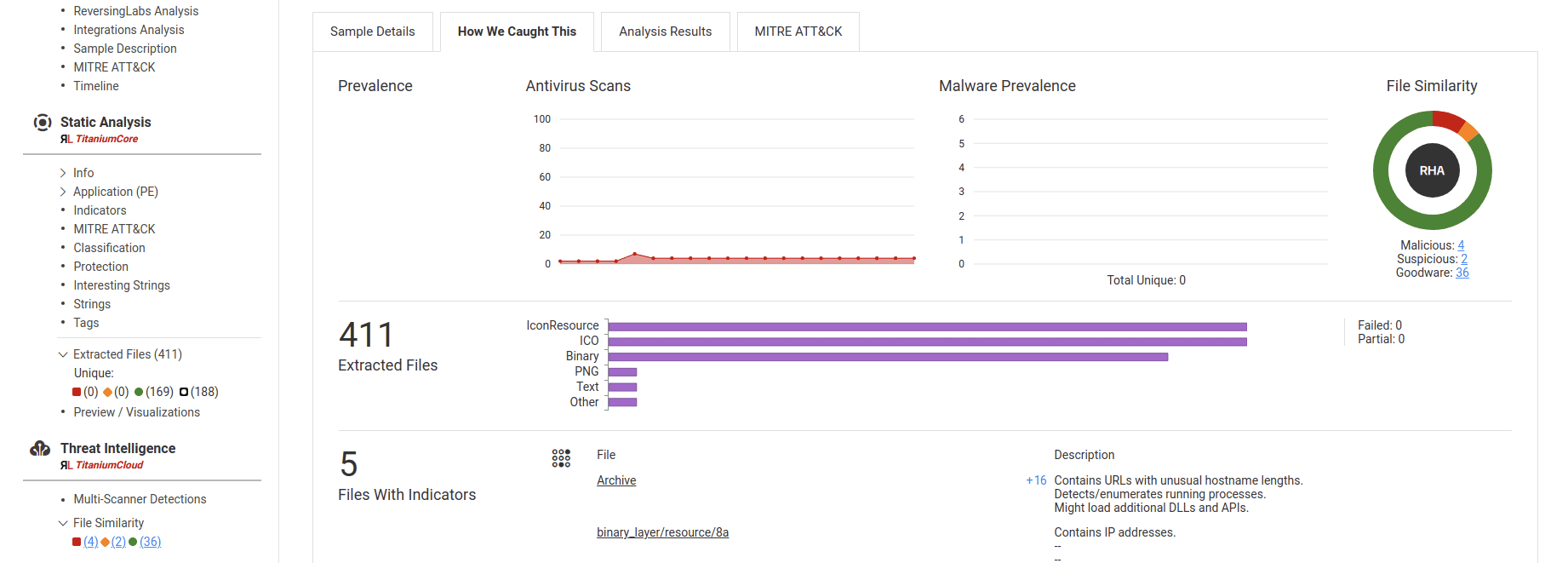
- Sample Details page - Next to links in the Extracted Files and File Similarity sections in the sample summary page sidebar menu, and in the How We Caught This > Prevalence > File Similarity subsection of the main sample summary report page
- Sample Details page - as colored symbols in URI stats for particular file types - for example, those containing Interesting strings, Network references or Malware configurations
What Determines the Classification of Samples?
A sample’s classification is determined from one of multiple different sources. All types of classification that a sample can receive on Spectra Analyze are described in detail in the Threat Classification Descriptions section.
The information about sample classification in the interface can be found in the expanded row on the Search Page.
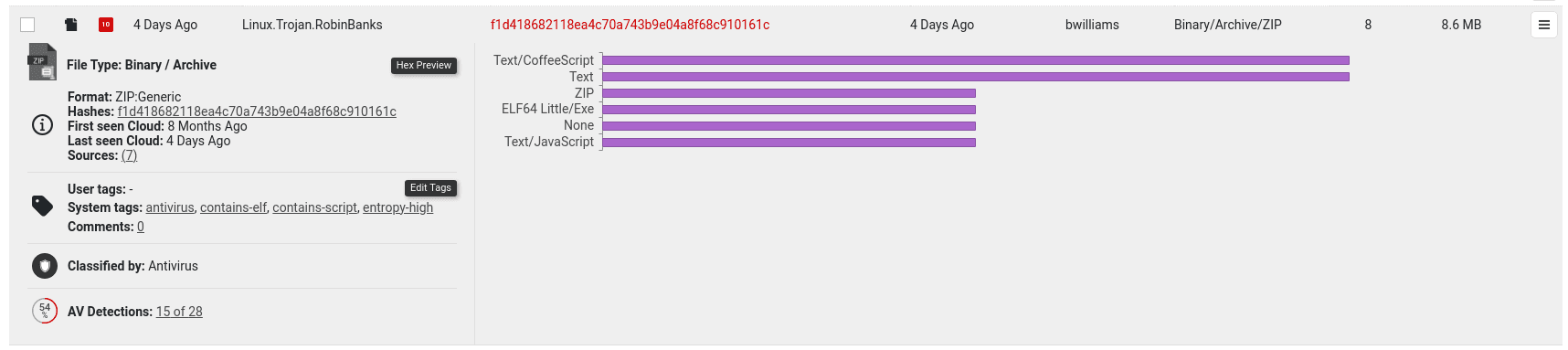
and in the Sample Details Summary section. If any files have been extracted from a sample, there will be additional information about the classification of extracted files.
Additional information about classification can be found in the Static Analysis > Classification section on the Sample Details page.
How to interpret analysis results?
The Sample Summary page highlights the most interesting information from the sample analysis report. It contains several sections with links to more detailed information.
The information on the Summary page will be different for every sample analyzed on the appliance, depending on the file type and classification status.
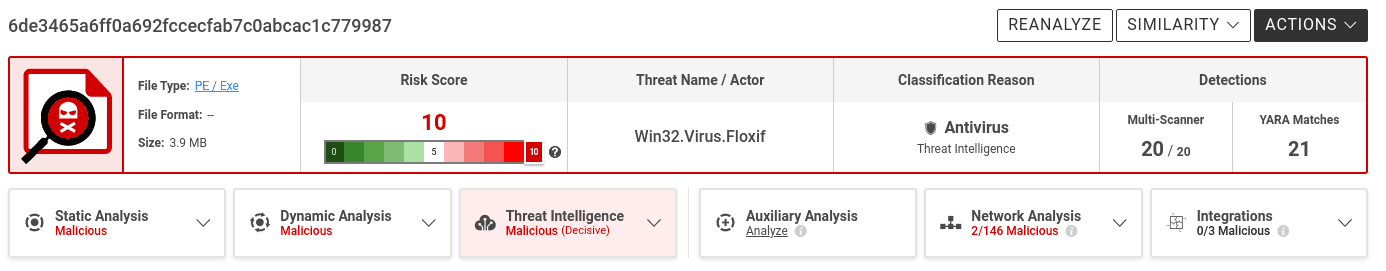
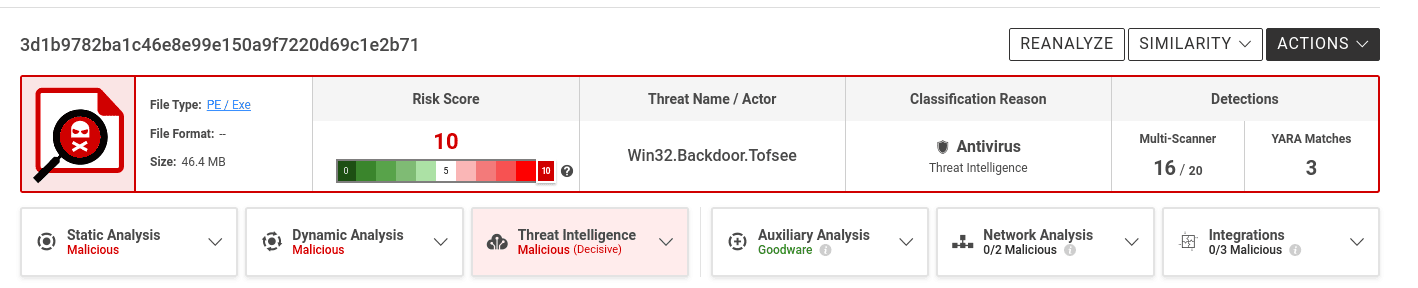
The most crucial information about the sample is curated in the header section of the page:
- the final classification (malicious / suspicious / goodware / no threats found) and the detected threat name
- risk score
- classification reason
- community threat detections count
- top 3 detected MITRE ATT&CK tactics
Spectra Analyze will always pick the most accurate classification as the final one and display this information in the Sample Summary header section. To properly read the final classification, users must consider and understand the classification reason and the risk score. The classification reason specifies which technology detected this threat. Files will usually have multiple detections from more than one classifier, but the classification reason tile is always the one that produced the final classification.
The final classification will always match one of the classifiers, but individual classifiers may have differing results between them. Due to differences in how different malicious samples and malware families behave, some samples might end up classified as malicious by one technology, and still be considered goodware by others. This doesn’t negate or diminish the final classification, it is the exact reason why Spectra Analyze uses multiple sources to classify files.
That’s also why overlooking the classification reason may result in confusion. For example, adding custom YARA rules to the Spectra Analyze is a powerful malware hunting feature, but improperly written rulesets can be too broad and result in a large number of samples suddenly getting classified as malicious by a YARA rule, even though everything else points to goodware.
Risk scores are assigned by the severity of the detected threat. Lesser threats like Adware will get a risk score of 6 (scores from 0-5 are reserved for goodware), while ransomware and trojans always get a risk score of 10.
Some users may choose to ignore lower risk classifications, such as Adware or Potentially Unwanted Applications (PUA), but those samples will still be classified as malicious to warn about potential threats, such as installers that have embedded adware.
In most cases, the results will be overwhelmingly biased towards a certain classification: a malicious file will be detected as such by Spectra Core and backed up by a large percentage (not necessarily 100%) of scanner detections. It will probably have an exact threat name, naming the malware type and/or the specific malware family. Certain file types might belong to a RHA File Similarity bucket with other malicious files. Even if such files get some negative results from specific technologies, it’s highly unlikely that they are not malicious.
On some occasions, a sample classified as goodware can still have some Spectra Intelligence scanner detections, but not enough to affect the final classification. These detections are most likely false positives, but users are still advised to check the scanner list to see which scanners detected a threat.
The classification of certain samples originates from samples extracted during analysis. It propagates from children to the parent, for example from a malicious executable file to the zip archive where it originated from. If this is the case, the description beneath the classification will highlight that it was based on an extracted file.
Classifications can also be overridden either through Goodware Overrides, where the classification of a high-trust parent sample is propagated down to extracted files, or manually by using the Spectra Analyze override feature.
In cases where the classification was set by the user, it will be considered final and displayed in the header, as well as in the table below. Local classification overrides will be visible as final to all appliance users, while the Spectra Intelligence overrides will additionally be synchronized with other appliances using the same Spectra Intelligence account, and other Spectra Intelligence accounts belonging to the same company, indicated by the middle segment of the username - u/company/user. In cases where a sample has both overrides, the local override will be displayed as the final classification.
In conclusion, while false detections are not impossible, they are much easier to identify if all of the important factors are considered and understood. For more information on each of these, refer to the Classifications, Risk Score and Threat Classification Sources chapters.
What is ReversingLabs Malware Naming Standard?
The ReversingLabs detection string consists of three main parts separated by dots. All parts of the string will always appear (all three parts are mandatory).
platform-subplatform.type.familyname
-
The first part of the string indicates the platform targeted by the malware.
This string is always one of the strings listed in the Platform string table. If the platform is Archive, Audio, ByteCode, Document, Image or Script, then it has a subplatform string. Platform and subplatform strings are divided by a hyphen (
-). The lists of available strings for Archive, Audio, ByteCode, Document, Image and Script subplatforms can be found in their respective tables. -
The second part of the detection string describes the malware type. Strings that appear as malware type descriptions are listed in the Type string table.
-
The third and last part of the detection string represents the malware family name, i.e. the name given to a particular malware strain.
Names "Agent", "Gen", "Heur", and other similar short generic names are not allowed. Names can't be shorter than three characters, and can't contain only numbers. Special characters (apart from
-) must be avoided as well. The-character is only allowed in exploit (CVE/CAN) names (for example CVE-2012-0158).
Examples
If a trojan is designed for the Windows 32-bit platform and has the family name "Adams", its detection string will look like this:
Win32.Trojan.Adams
If some backdoor malware is a PHP script with the family name "Jones", the detection string will look like this:
Script-PHP.Backdoor.Jones
Some potentially unwanted application designed for Android that has the family name "Smith" will have the following detection string:
Android.PUA.Smith
Some examples of detections with invalid family names are:
Win32.Dropper.Agent
ByteCode-MSIL.Keylogger.Heur
Script-JS.Hacktool.Gen
Android.Backdoor.12345
Document-PDF.Exploit.KO
Android.Spyware.1a
Android.Spyware.Not-a-CVE
Win32.Trojan.Blue_Banana
Win32.Ransomware.Hydra:Crypt
Win32.Ransomware.HDD#Cryptor
Platform string
The platform string indicates the operating system that the malware is designed for. The following table contains the available strings and the operating systems for which they are used.
| String | Short description |
|---|---|
| ABAP | SAP / R3 Advanced Business Application Programming environment |
| Android | Applications for Android OS |
| AOL | America Online environment |
| Archive | Archives. See Archive subplatforms for more information. |
| Audio | Audio. See Audio subplatforms for more information. |
| BeOS | Executable content for Be Inc. operating system |
| Boot | Boot, MBR |
| Binary | Binary native type |
| ByteCode | ByteCode, platform-independent. See ByteCode subplatforms for more information. |
| Blackberry | Applications for Blackberry OS |
| Console | Executables or applications for old consoles (e.g. Nintendo, Amiga, ...) |
| Document | Documents. See Document subplatforms for more information. |
| DOS | DOS, Windows 16 bit based OS |
| EPOC | Applications for EPOC mobile OS |
| Emails. See Email subplatforms for more information. | |
| Firmware | BIOS, Embedded devices (mp3 players, ...) |
| FreeBSD | Executable content for 32-bit and 64-bit FreeBSD platforms |
| Image | Images. See Image subplatforms for more information. |
| iOS | Applications for Apple iOS (iPod, iPhone, iPad…) |
| Linux | Executable content for 32 and 64-bit Linux operating systems |
| MacOS | Executable content for Apple Mac OS, OS X |
| Menuet | Executable content for Menuet OS |
| Novell | Executable content for Novell OS |
| OS2 | Executable content for IBM OS/2 |
| Package | Software packages. See Package subplatforms for more information. |
| Palm | Applications for Palm mobile OS |
| Script | Scripts. See Script subplatforms for more information. |
| Shortcut | Shortcuts |
| Solaris | Executable content for Solaris OS |
| SunOS | Executable content for SunOS platform |
| Symbian | Applications for Symbian OS |
| Text | Text native type |
| Unix | Executable content for the UNIX platform |
| Video | Videos |
| WebAssembly | Binary format for executable code in Web pages |
| Win32 | Executable content for 32-bit Windows OS's |
| Win64 | Executable content for 64-bit Windows OS's |
| WinCE | Executable content for Windows Embedded Compact OS |
| WinPhone | Applications for Windows Phone |
Archive subplatforms
| String | Short description |
|---|---|
| ACE | WinAce archives |
| AR | AR archives |
| ARJ | ARJ (Archived by Robert Jung) archives |
| BZIP2 | Bzip2 archives |
| CAB | Microsoft Cabinet archives |
| GZIP | GNU Zip archives |
| ISO | ISO image files |
| JAR | JAR (Java ARchive) archives |
| LZH | LZH archives |
| RAR | RAR (Roshal Archive) archives |
| 7ZIP | 7-Zip archives |
| SZDD | Microsoft SZDD archives |
| TAR | Tar (tarball) archives |
| XAR | XAR (eXtensible ARchive) archives |
| ZIP | ZIP archives |
| ZOO | ZOO archives |
| Other Archive identification | All other valid Spectra Core identifications of Archive type |
Audio subplatforms
| String | Short description |
|---|---|
| WAV | Wave Audio File Format |
| Other Audio identification | All other valid Spectra Core identifications of Audio type |
ByteCode subplatforms
| String | Short description |
|---|---|
| JAVA | Java bytecode |
| MSIL | MSIL bytecode |
| SWF | Adobe Flash |
Document subplatforms
| String | Short description |
|---|---|
| Access | Microsoft Office Access |
| CHM | Compiled HTML |
| Cookie | Cookie files |
| Excel | Microsoft Office Excel |
| HTML | HTML documents |
| Multimedia | Multimedia containers that aren't covered by other platforms (e.g. ASF) |
| Office | File that affects multiple Office components |
| OLE | Microsoft Object Linking and Embedding |
| PDF documents | |
| PowerPoint | Microsoft Office PowerPoint |
| Project | Microsoft Office Project |
| Publisher | Microsoft Office Publisher |
| RTF | RTF documents |
| Visio | Microsoft Office Visio |
| XML | XML and XML metafiles (ASX) |
| Word | Microsoft Office Word |
| Other Document identification | All other valid Spectra Core identifications of Document type |
Email subplatforms
| String | Short description |
|---|---|
| MIME | Multipurpose Internet Mail Extensions |
| MSG | Outlook MSG file format |
Image subplatforms
| String | Short description |
|---|---|
| ANI | File format used for animated mouse cursors on Microsoft Windows |
| BMP | Bitmap images |
| EMF | Enhanced Metafile images |
| EPS | Adobe Encapsulated PostScript images |
| GIF | Graphics Interchange Format |
| JPEG | JPEG images |
| OTF | OpenType Font |
| PNG | Portable Network Graphics |
| TIFF | Tagged Image File Format |
| TTF | Apple TrueType Font |
| WMF | Windows Metafile images |
| Other Image identification | All other valid Spectra Core identifications of Image type |
Package subplatforms
| String | Short description |
|---|---|
| NuGet | NuGet packages |
| DEB | Debian Linux DEB packages |
| RPM | Linux RPM packages |
| WindowStorePackage | Packages for distributing and installing Windows apps |
| Other Package identification | All other valid Spectra Core identifications of Package type |
Script subplatforms
| String | Short description |
|---|---|
| ActiveX | ActiveX scripts |
| AppleScript | AppleScript scripts |
| ASP | ASP scripts |
| AutoIt | AutoIt scripts (Windows) |
| AutoLISP | AutoCAD LISP scripts |
| BAT | Batch scripts |
| CGI | CGI scripts |
| CorelDraw | CorelDraw scripts |
| Ferite | Ferite scripts |
| INF | INF Script, Windows installer scripts |
| INI | INI configuration file |
| IRC | IRC, mIRC, pIRC/Pirch Script |
| JS | Javascript, JScript |
| KiXtart | KiXtart scripts |
| Logo | Logo scripts |
| Lua | Lua scripts |
| Macro | Macro (e.g. VBA, AmiPro macros, Lotus123 macros) |
| Makefile | Makefile configuration |
| Matlab | Matlab scripts |
| Perl | Perl scripts |
| PHP | PHP scripts |
| PowerShell | PowerShell scripts, Monad (MSH) |
| Python | Python scripts |
| Registry | Windows Registry scripts |
| Ruby | Ruby scripts |
| Shell | Shell scripts |
| Shockwave | Shockwave scripts |
| SQL | SQL scripts |
| SubtitleWorkshop | SubtitleWorkshop scripts |
| WinHelp | WinHelp Script |
| WScript | Windows Scripting Host related scripts (can be VBScript, JScript, …) |
| Other Script identification | All other valid Spectra Core identifications of Script type |
Type string
This string is used to describe the general type of malware. The following table contains the available strings and describes what each malware type is capable of.
| String | Description |
|---|---|
| Adware | Presents unwanted advertisements |
| Backdoor | Bypasses device security and allows remote access |
| Browser | Browser helper objects, toolbars, and malicious extensions |
| Certificate | Classification derived from certificate data |
| Coinminer | Uses system resources for cryptocurrency mining without the user's permission |
| Dialer | Applications used for war-dialing and calling premium numbers |
| Downloader | Downloads other malware or components |
| Dropper | Drops malicious artifacts including other malware |
| Exploit | Exploits for various vulnerabilities, CVE/CAN entries |
| Format | Malformations of the file format. Classification derived from graylisting, validators on unpackers |
| Hacktool | Software used in hacking attacks, that might also have a legitimate use |
| Hyperlink | Classifications derived from extracted URLs |
| Infostealer | Steals personal info, passwords, etc. |
| Keylogger | Records keystrokes |
| Malware | New and recently discovered malware not yet named by the research community |
| Network | Networking utilities, such as tools for DoS, DDoS, etc. |
| Packed | Packed applications (UPX, PECompact…) |
| Phishing | Email messages (or documents) created with the aim of misleading the victim by disguising itself as a trustworthy entity into opening malicious links, disclosing personal information or opening malicious files. |
| PUA | Potentially unwanted applications (hoax, joke, misleading...) |
| Ransomware | Malware which encrypts files and demands money for decryption |
| Rogue | Fraudulent AV installs and scareware |
| Rootkit | Provides undetectable administrator access to a computer or a mobile device |
| Spam | Other junk mail that does not unambiguously fall into the Phishing category, but contains unwanted or illegal content. |
| Spyware | Collects personal information and spies on users |
| Trojan | Allows remote access, hides in legit applications |
| Virus | Self-replicating file/disk/USB infectors |
| Worm | Self-propagating malware with exploit payloads |