Air‑Gapped Malware Analysis with Spectra Analyze and T1000
Organizations operating in high‑security environments often require the ability to analyze potentially malicious files without exposing internal networks to external connectivity.
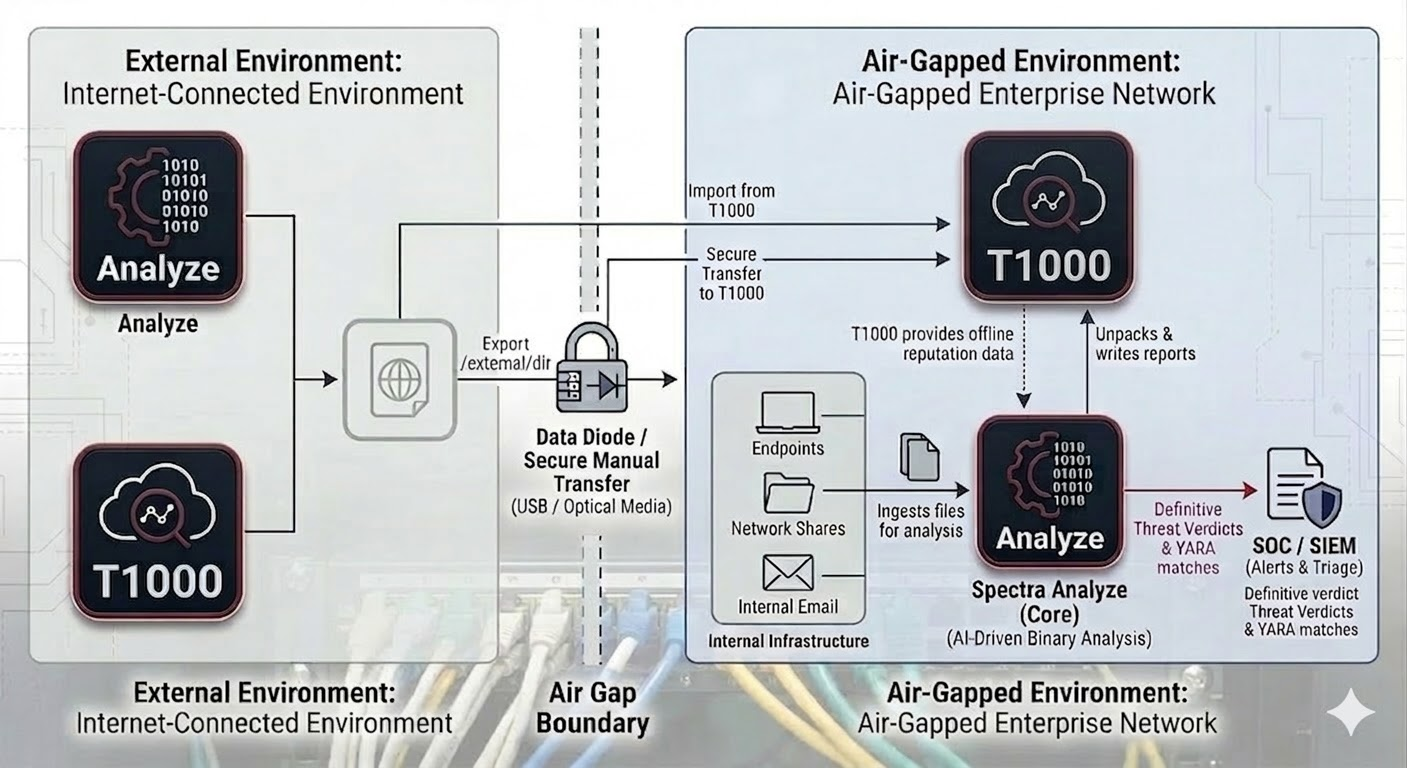
ReversingLabs Spectra Analyze, combined with the T1000 threat intelligence appliance, enables organizations to perform deep malware analysis within fully isolated or air‑gapped environments.
Spectra Analyze performs complex binary analysis on submitted files using the Spectra Core analysis engine, while the T1000 appliance provides locally hosted reputation and threat intelligence data derived from the Spectra Intelligence dataset.
Together, these components enable organizations to investigate suspicious files, generate detailed analysis reports, and classify threats without requiring direct access to external cloud services.
This architecture supports secure malware analysis workflows for government, defense, and other highly regulated environments where strict network isolation is required.
Solution Overview
The ReversingLabs air‑gapped malware analysis solution combines Spectra Analyze with the T1000 intelligence appliance to deliver deep file analysis capabilities inside restricted environments.
Spectra Analyze is deployed as the primary malware analysis platform. Files submitted by analysts, automated workflows, or security tools are ingested by the platform, decomposed to expose embedded objects, and analyzed using the Spectra Core static analysis engine.
During analysis, Spectra Analyze can query the locally deployed T1000 appliance for reputation and classification information. Because both components operate within the same restricted network, the analysis workflow can function without requiring connectivity to external intelligence services.
Key Capabilities
- Deep static malware analysis using the Spectra Core engine
- Extraction and analysis of nested or embedded files
- Local threat intelligence and reputation lookups through the T1000 appliance
- Detailed analysis reports containing classification, indicators, and metadata
- API access for integration with security operations workflows
- Deployment within isolated or air‑gapped network environments
Architecture
The solution architecture consists of two primary components deployed within a protected network environment.
Spectra Analyze serves as the analysis platform responsible for file ingestion, decomposition, and static analysis. The system analyzes submitted files and generates structured analysis results.
T1000 is deployed as a local threat intelligence appliance that provides reputation and classification information. During analysis workflows, Spectra Analyze queries the T1000 system for intelligence data used to enrich analysis results.
This architecture allows organizations to operate malware analysis capabilities within restricted networks while maintaining access to locally hosted intelligence data.
Analysis Workflow
- A file is submitted to Spectra Analyze through the user interface or API.
- The platform ingests the file and extracts embedded objects and nested content.
- Static analysis is performed using the Spectra Core analysis engine.
- Spectra Analyze queries the local T1000 appliance for reputation and threat classification data.
- The platform generates a detailed analysis report containing indicators and classification information.
- Analysts review results through the interface or integrate them with other security tools using APIs.
Deployment Model
The solution can be deployed within isolated network environments where direct internet connectivity is restricted or prohibited.
Typical deployment characteristics include:
- Analysis infrastructure located within a protected network segment
- Restricted administrative access to analysis systems
- Controlled submission interfaces for analysts and automated workflows
- Local intelligence provided by the T1000 appliance
This model allows organizations to safely analyze potentially malicious files while maintaining strict network isolation policies.
Operational Considerations
Spectra Analyze and the T1000 appliance can be maintained through periodic offline updates delivered according to the organization's established maintenance and security procedures, for example ReversingLabs can ship disk containing the updates.
Use Cases
- Government Security Operations Centers (SOCs): Security teams can analyze suspicious files submitted by analysts, endpoint security tools, or incident response workflows while maintaining strict network isolation.
- Defense and Classified Networks: The architecture enables malware investigation capabilities within environments where external connectivity is restricted or prohibited.
- High‑Security Enterprise Environments: Organizations responsible for protecting sensitive data or critical infrastructure can deploy a dedicated malware analysis capability within controlled network environments.
Conclusion
ReversingLabs Spectra Analyze combined with the T1000 intelligence appliance provides organizations with the ability to perform deep malware analysis within restricted or air‑gapped environments.
By combining complex binary analysis with locally hosted intelligence data, the solution enables security teams to investigate suspicious files, classify threats, and generate detailed analysis reports without requiring external connectivity.
This deployment model supports organizations that must maintain strict network isolation while still requiring advanced malware analysis capabilities.
